
Nmap Tutorial For Beginners | How to Scan Your Network Using Nmap | Ethical Hacking Tool | Edureka - YouTube

Can hacks become hackers? What I learned exploiting websites with pros | Data and computer security | The Guardian

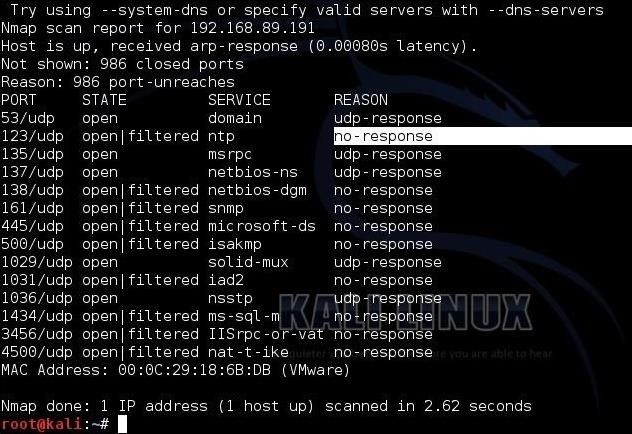
Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan | Infosec Resources
![Nmap evade firewall and scripting [updated 2019] | Infosec Resources Nmap evade firewall and scripting [updated 2019] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/082912_1952_NmapEvadeFi2.jpg)





![Nmap from beginner to advanced [updated 2021] | Infosec Resources Nmap from beginner to advanced [updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/2019/02/020921-1.jpg)










![Use Nmap for Tactical Network Reconnaissance [Tutorial] - YouTube Use Nmap for Tactical Network Reconnaissance [Tutorial] - YouTube](https://i.ytimg.com/vi/ltEFbi_I2KY/maxresdefault.jpg)
![Nmap evade firewall and scripting [updated 2019] | Infosec Resources Nmap evade firewall and scripting [updated 2019] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/082912_1952_NmapEvadeFi1.jpg)

