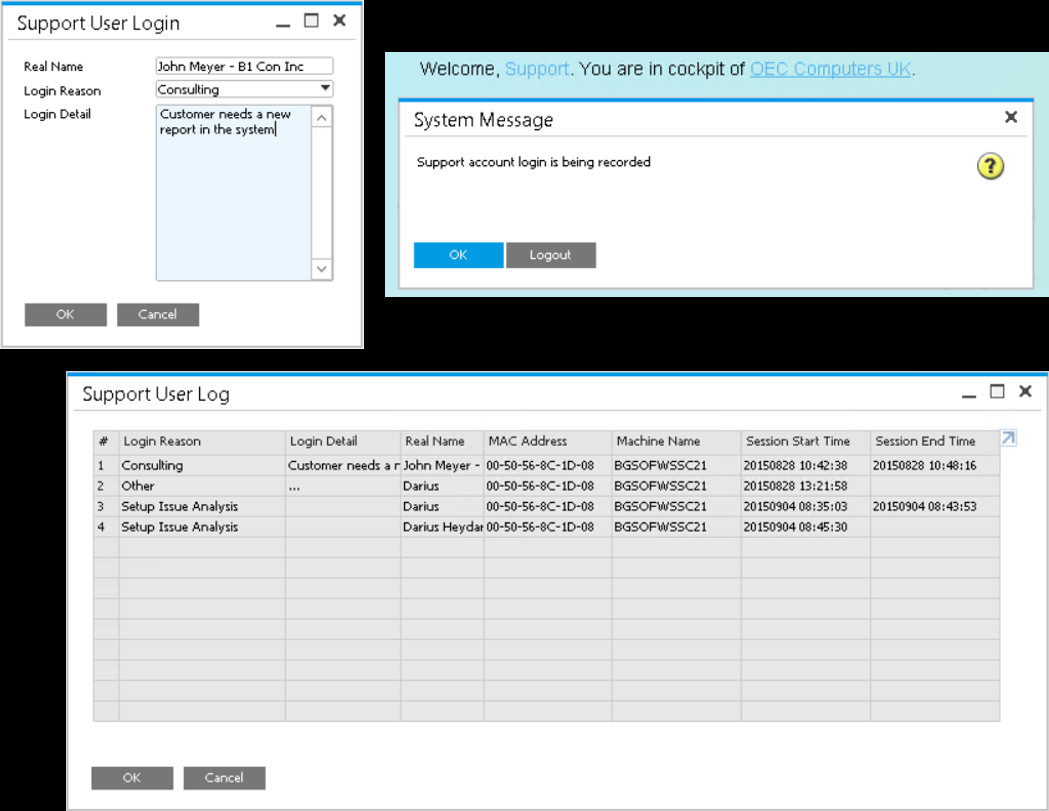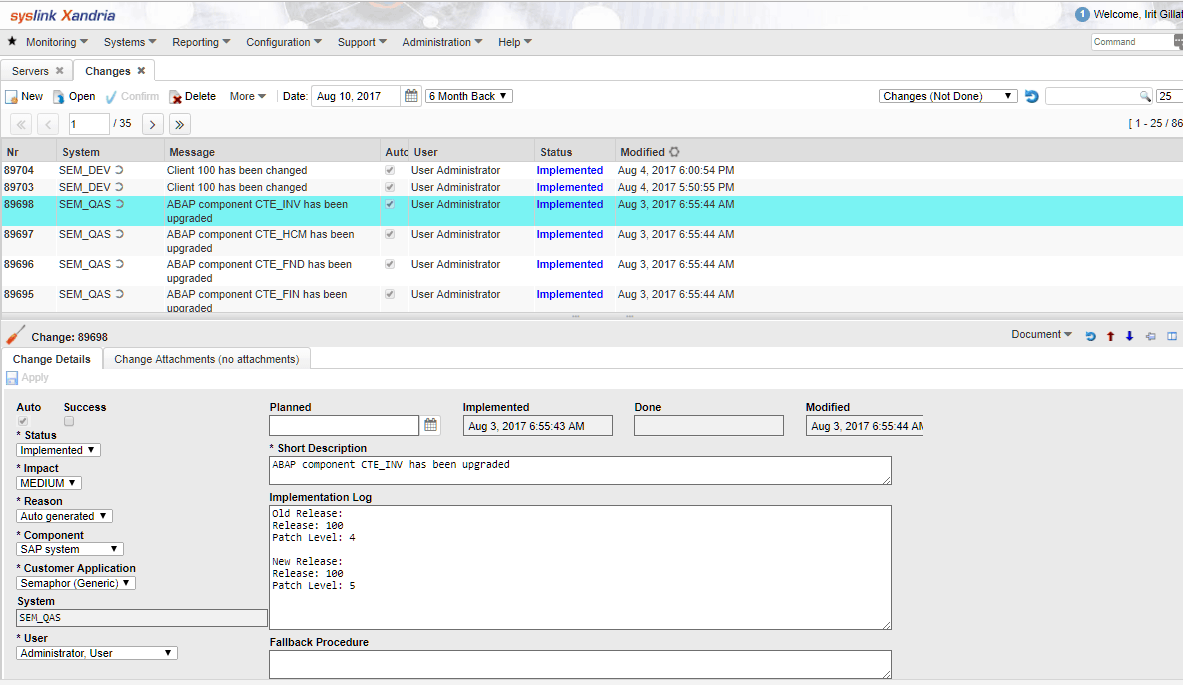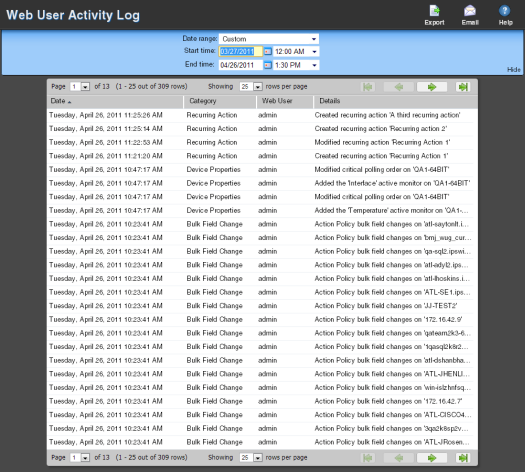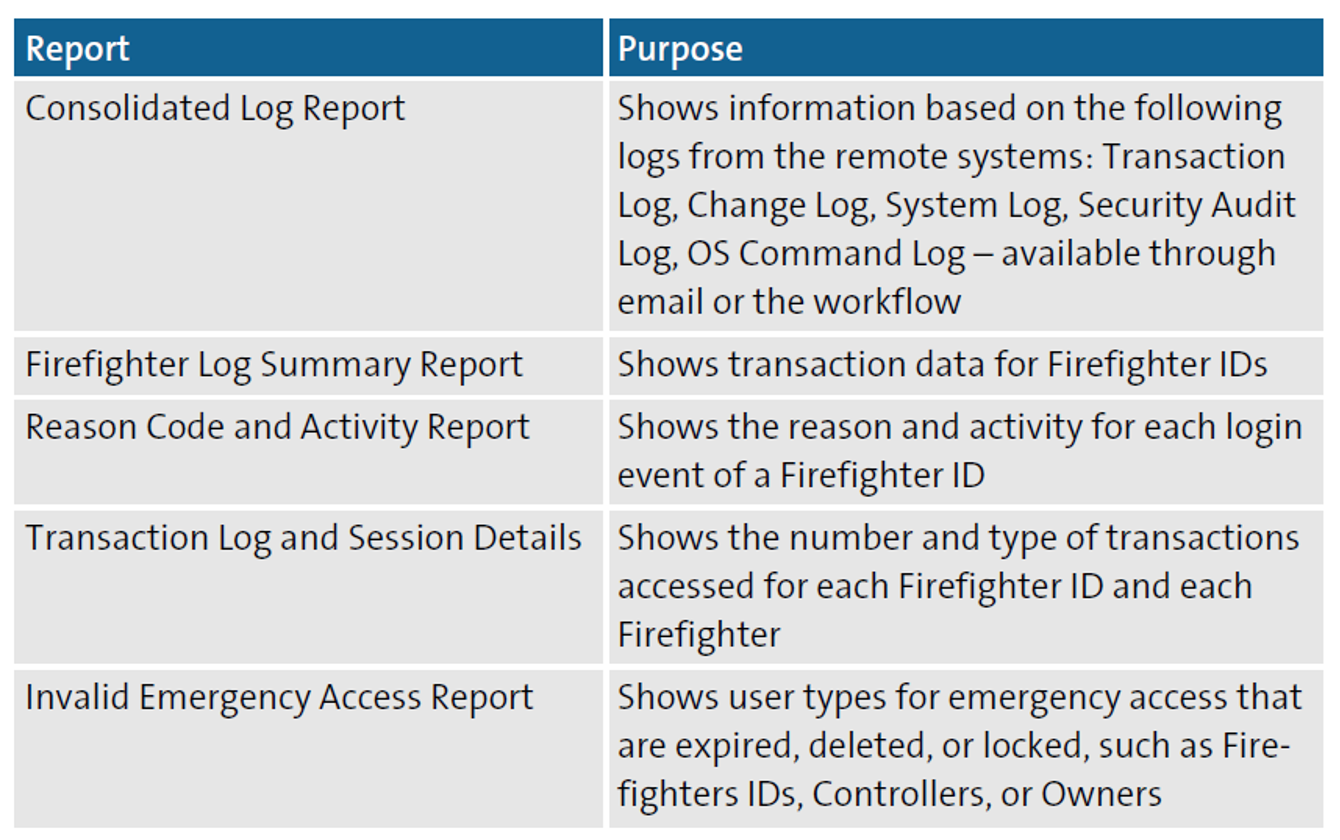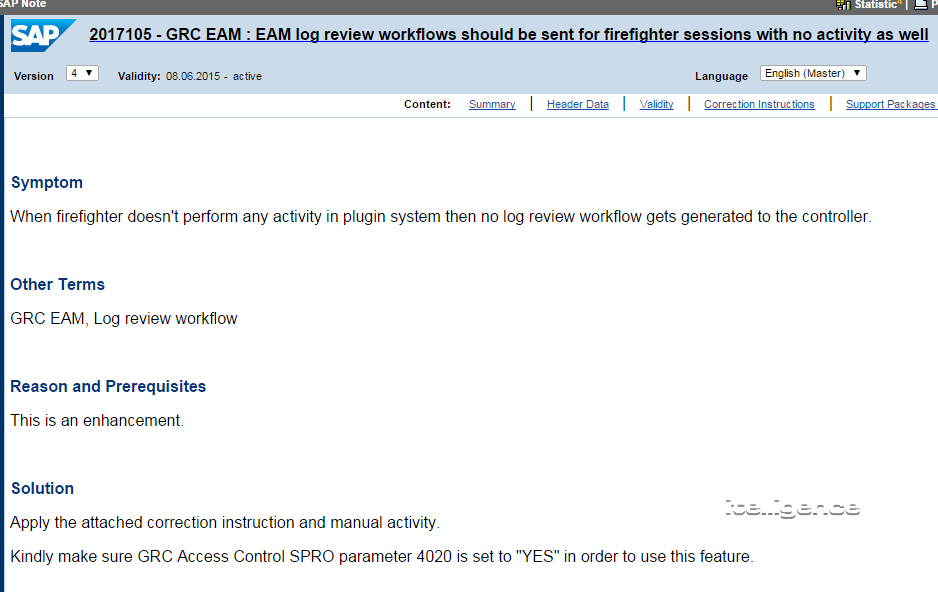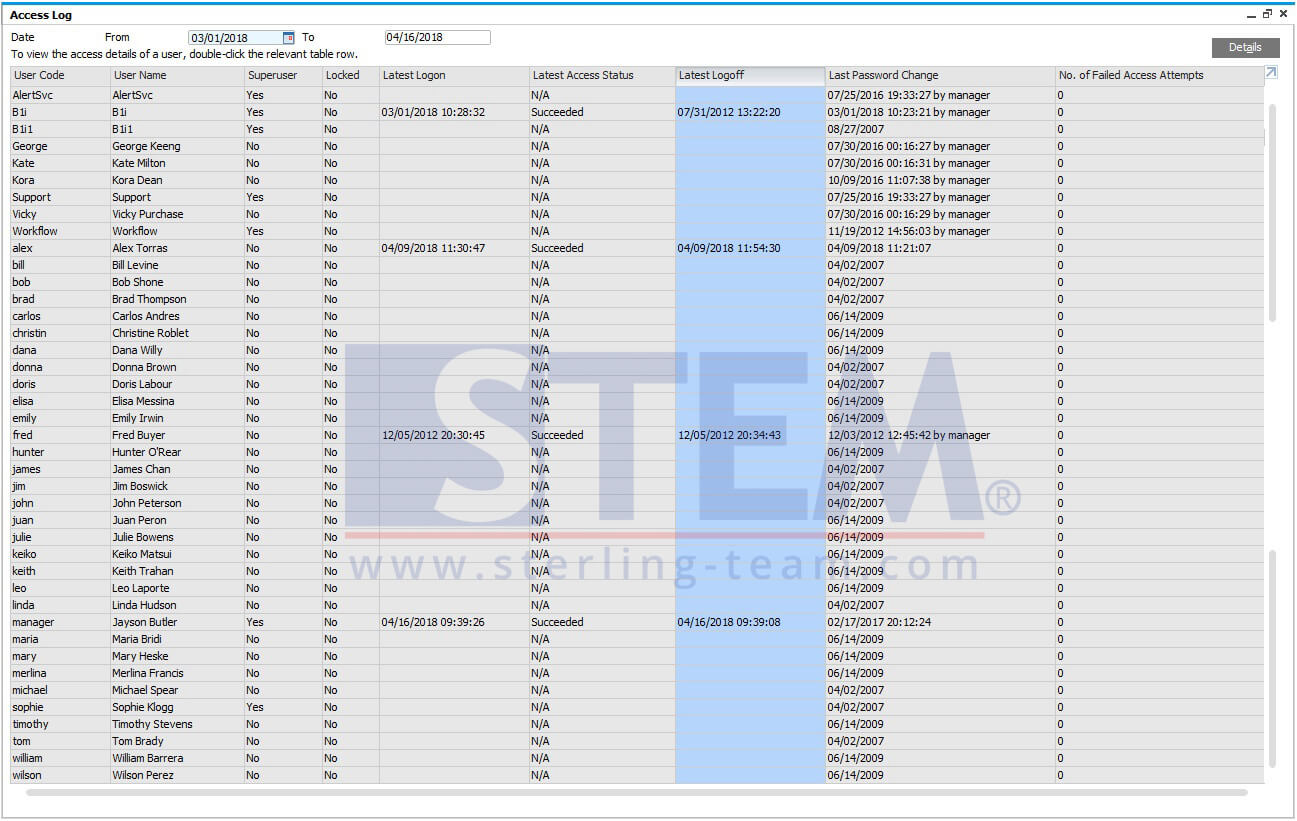
Monitoring Access Log & Change Log for Identify User Access | SAP Business One Indonesia Tips | STEM SAP Gold Partner
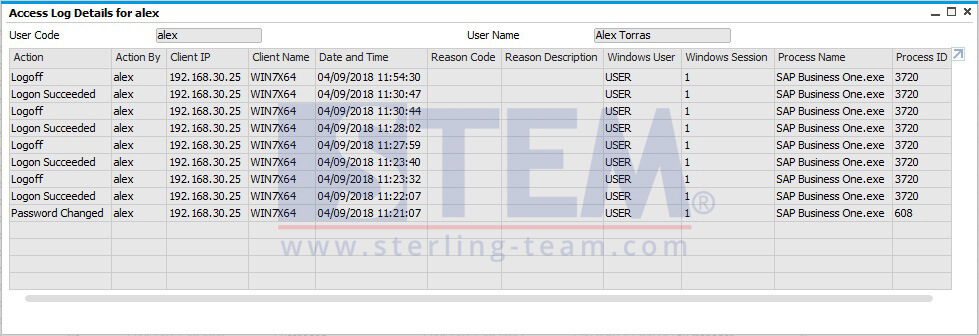
Monitoring Access Log & Change Log for Identify User Access | SAP Business One Indonesia Tips | STEM SAP Gold Partner
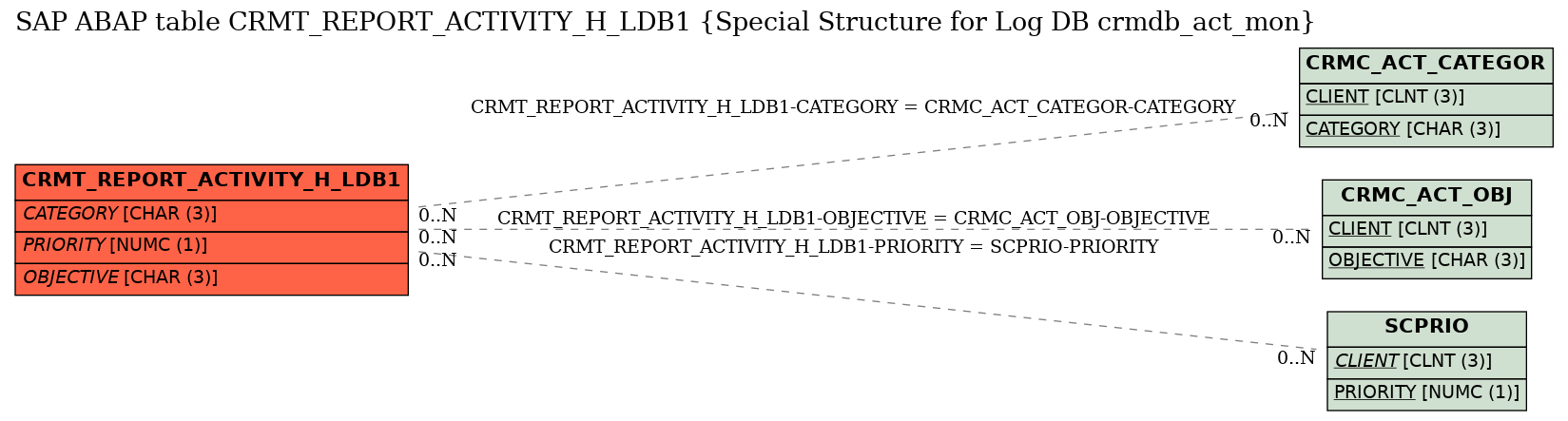
SAP ABAP Table CRMT_REPORT_ACTIVITY_H_LDB1 (Special Structure for Log DB crmdb_act_mon), sap-tables.org - The Best Online document for SAP ABAP Tables

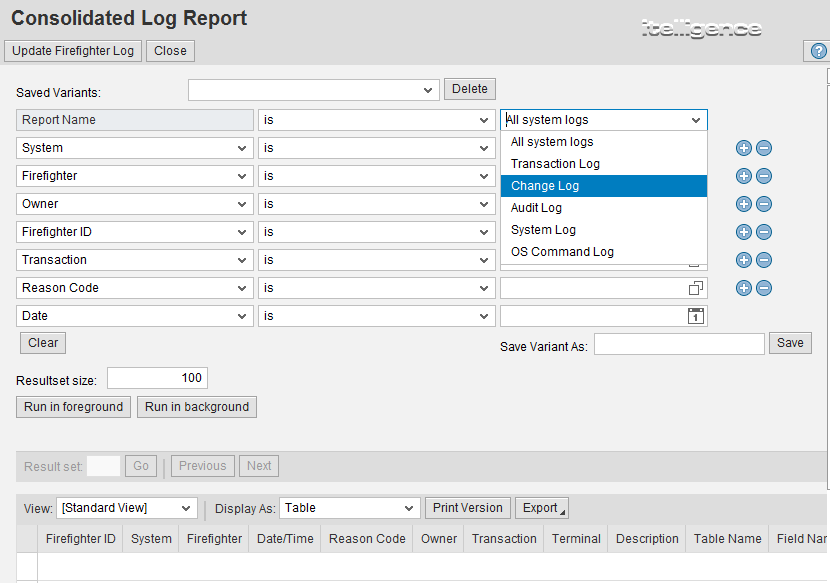
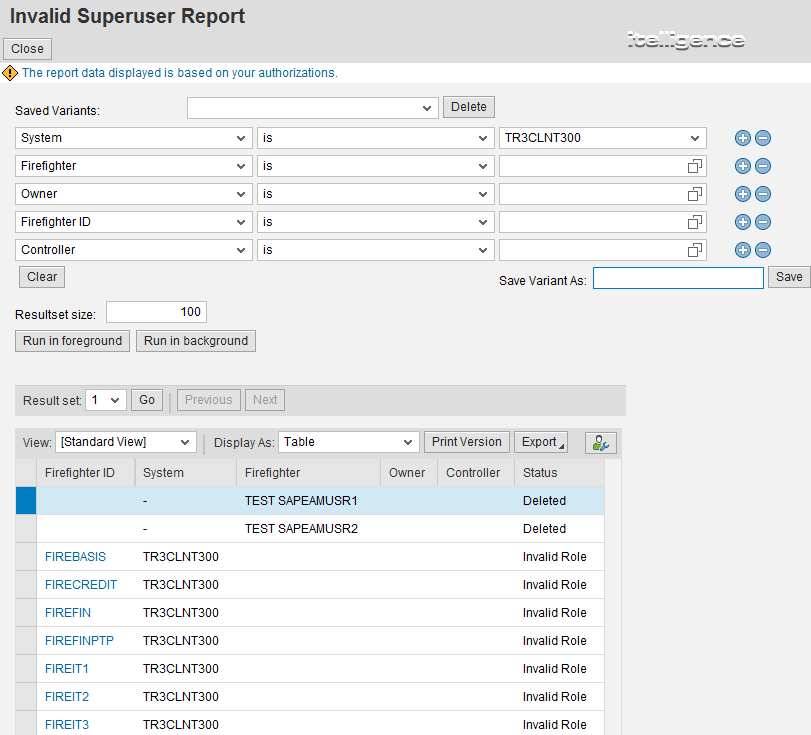
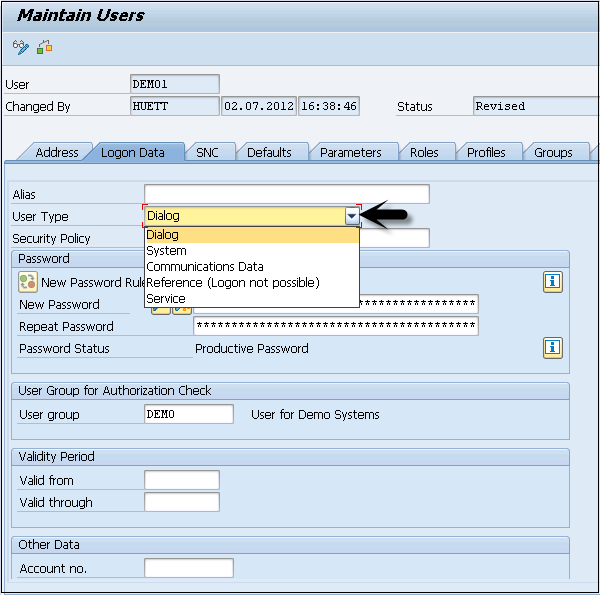
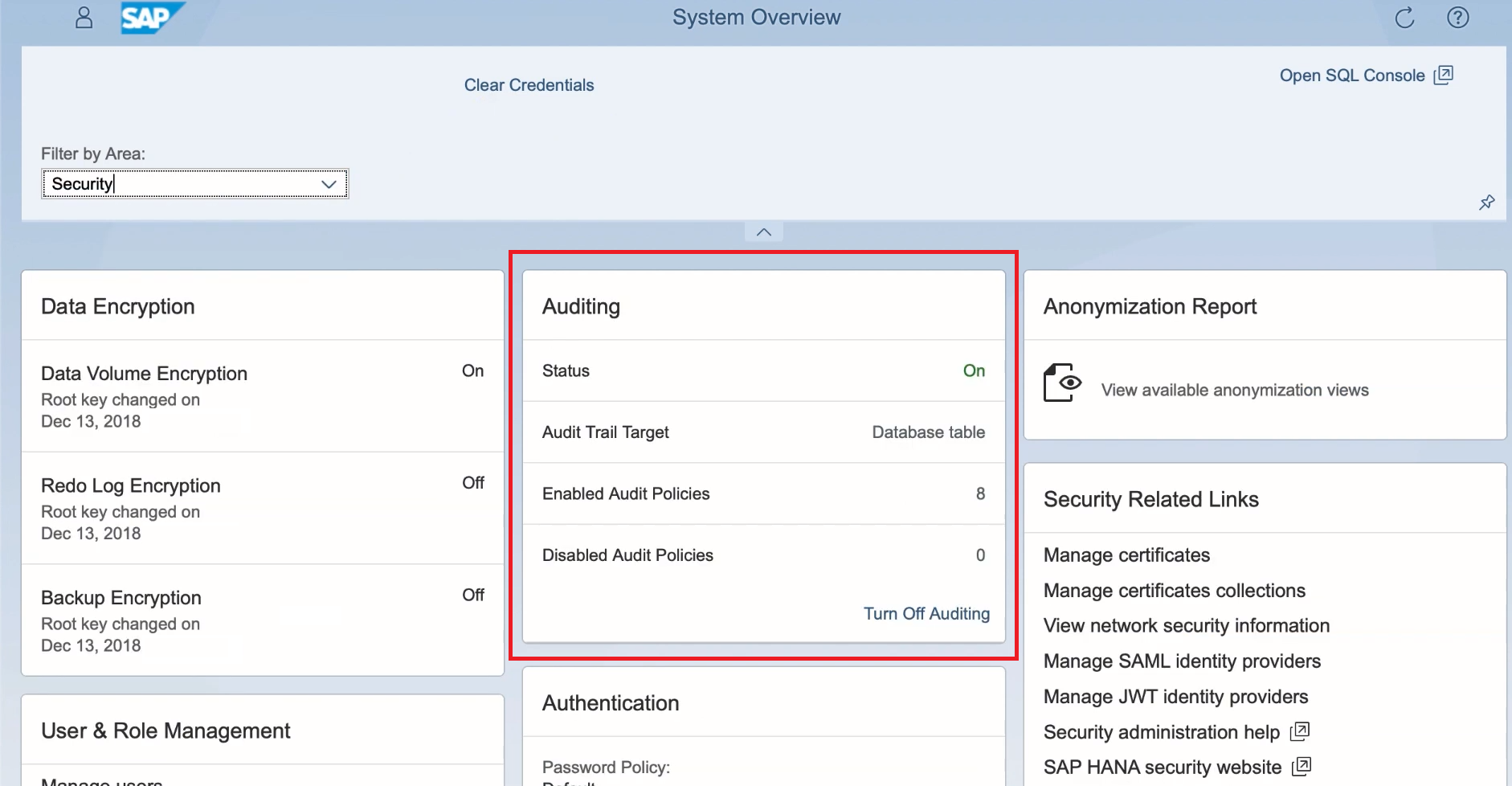
Analysis and Recommended Settings of the Security Audit Log (SM19 / RSAU_CONFIG, SM20 / RSAU_READ_LOG) | SAP Blogs

SAP Security Audit Logs: Which event types should I enable? There are 90 of them! And how much disk space do I need? | SAP Blogs
SAP ABAP Table BBPD_LA_ACTIVITY (User activities log) - SAP Datasheet - The Best Online SAP Object Repository
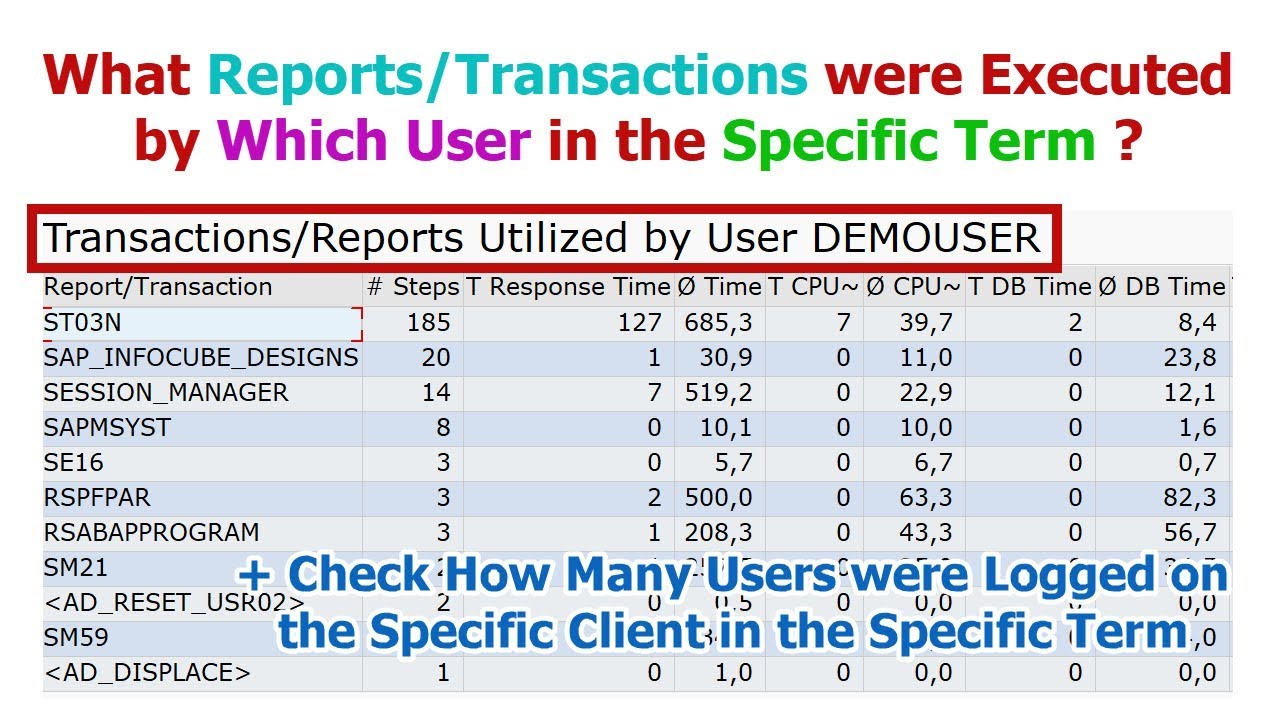
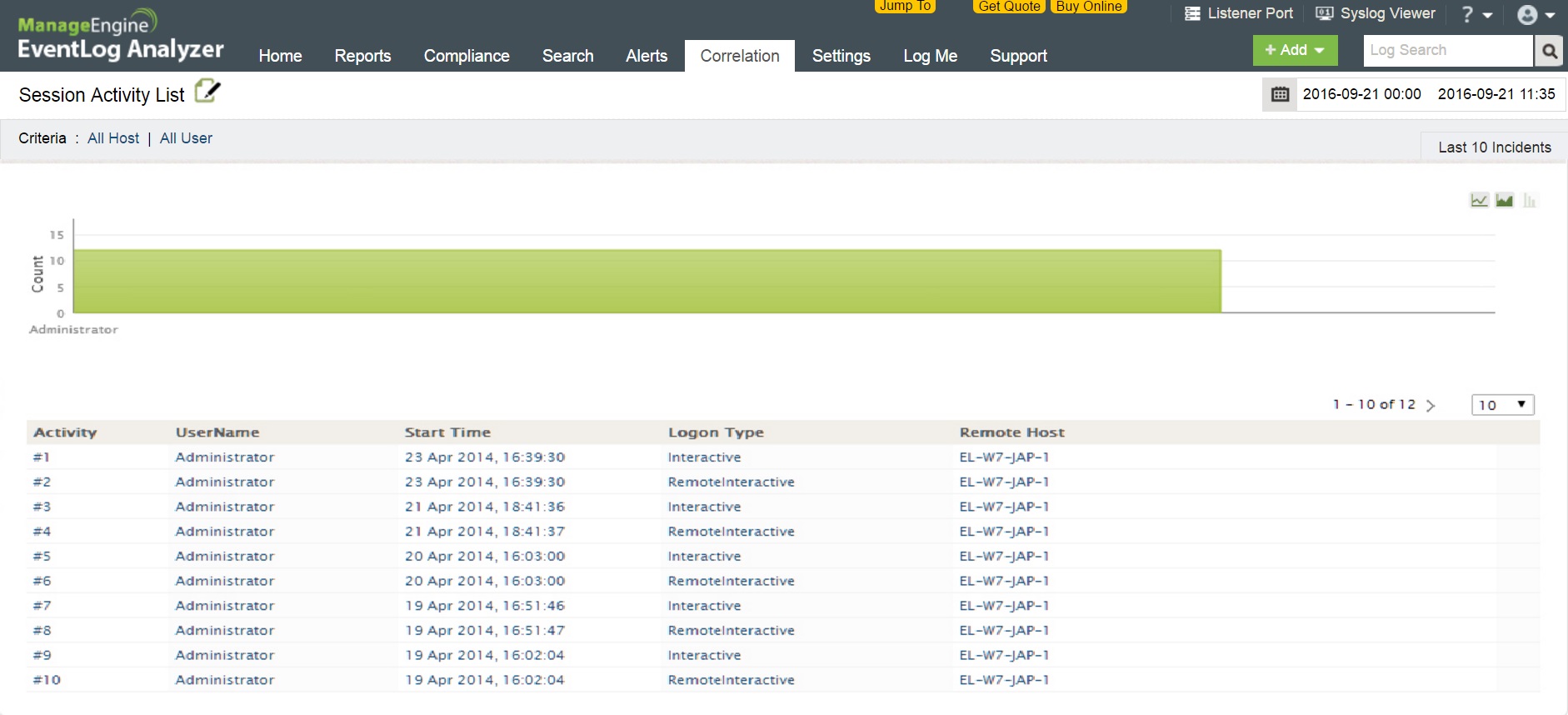
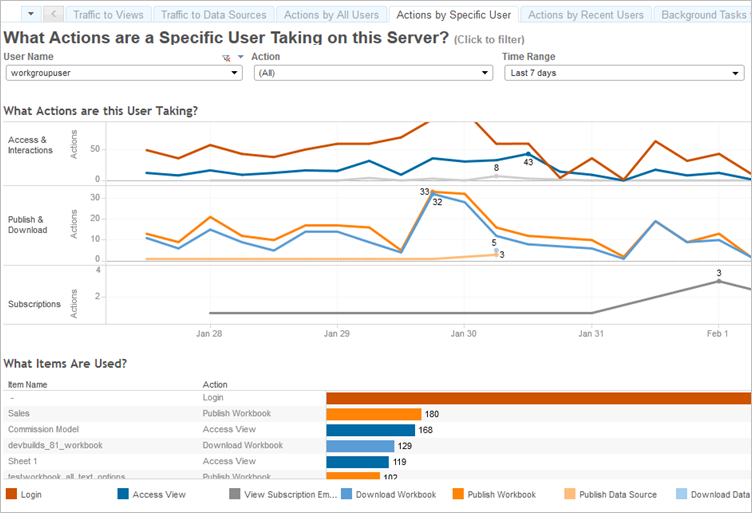
SAP: Finding Reports/Transactions Executed By the Specific User in the Specific Term (in ST03N) - YouTube